THE DARK HEART OF THE DARK WEB
Whether it’s drugs, human trafficking, theft of intellectual property or personally identifiable information (PII), or any other criminal activity you can think of, the Dark Web is the playground of today’s cybercriminals. It is where any company, small or large, whose credentials have been compromised, will find them openly for sale to the highest bidder. And that person plans to use them against you.
Worse still, you won’t even know your credentials are for sale on the Dark Web until it’s too late; you’ve been breached!
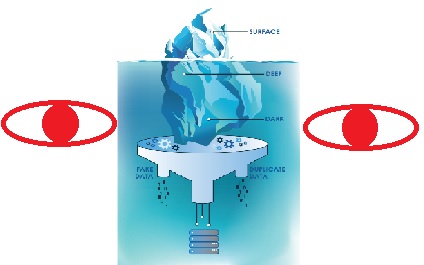
Below are some statistics on attacks on small-to-medium sized businesses (SMBs):
HOW DO THEY GET MY CREDENTIALS?
Employees use their work email to access other businesses all of the time; for work and for pleasure. These sites, like those below, are out of your control and may or may not have proper security measures to protect them; leaving your business vulnerable to a breach.
Where information is stolen from:
- Email Services
- HR & Payroll
- Banking
- CRM
- Travel Sites
- Social Media
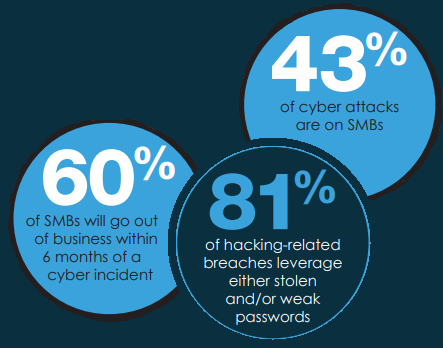
Below is a graphic showing which attributes are most often tracked and stolen:
DEEPER INTO THE DARK WEB
The last few years have seen an increasing number of data breaches, as hackers, organized criminals, and nation- states attack companies and individuals around the world. Stolen personal data is sold in black markets; Billions of personally identifiable information (PII), sensitive data and usernames and passwords are published, and terabytes of documents are exposed in the deep and dark web.
This is impacting consumer trust, brand loyalty, and engagement as well as powering account takeovers, financial fraud, and other criminal activity. Reduce the risks created from exposed identity information found in open sources on the surface, social, deep and dark web.
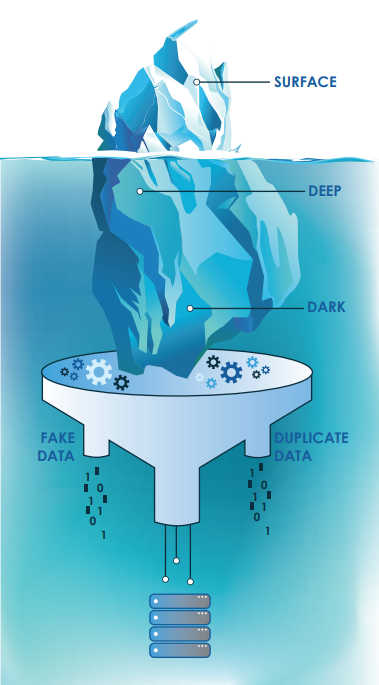
While the number of accumulated raw identity records provides insight into the sheer volume of data points out there, it is not the best indicator of overall risk. This is because not all of the data gathered is authentic or unique. Circulating in the Darknet and mixed in with authentic breach corpuses, are fake breaches and “combo-lists” or mashups of different breach packages. In addition, attribution is all too often not clear, so it may not be obvious where the data came from and which site was actually breached.
Misattribution incidents – like the 2016 event, when a breach attributed to Dropbox was actually from Tumblr - create anxiety for consumers, costly loads on call centers, and potential legal liability for service providers.
HOW CAN I PROTECT MY BUSINESS?
Dark Web Monitoring can detect if your company’s credentials have been compromised, protecting you from the risks those websites pose in exposing them.
If you are concerned information has been compromised for your place of business, contact America One to request a FREE Cyber Security assessment (a $299 value), which features a free Dark Web Scan (a $40 value). We will let you know where your IT security infrastructure stands when it comes to information security and suggest remedies to protect you from an unexpected attack. Make sure you have the adequate protections in place to detect and deter cyber security threats. Call America One at (781) 356-3535 or schedule a 10-minute call below to request your FREE assessment today.