When you hear about phishing scams, you might picture someone falling for a Nigerian prince scheme they get sent over email or possibly the robocalls you tend to get during tax season. But did you know that such scams are also being conducted by cybercriminals over nearly all social media platforms?
One case study observed a series of attacks against several companies (across multiple social platforms) across MENA in 2017 (the Middle East and North Africa). A fake profile operating under the name Mia Ash would target businesses it deemed susceptible to cybercriminal activity. These attacks date from April 2016 all the way until July, over a year later.
The Mia Ash profiles operated first and foremost as a catfishing scheme. Catfishing is a term that’s been gaining recognition since 2010. What happens is that a person or a group of people create a profile under a false name and with false pictures. This usually also involves elaborate backstories to uphold their fake identity and make it seem more credible, in order to steal your information or money.
Mia Ash would start by choosing a company to target and then reaching out to several different employees there. ‘She’ would then establish cordial relationships with them under the fake name and pictures. This was made easier by creating several Mia Ash accounts across multiple social media platforms, like WhatsApp and Facebook, making the profiles appear more legitimate and to further their reach.

‘She’ operated primarily on LinkedIn as her way of reaching out to members of a targeted business, and she would get these employees to accept her contact requests and slowly gain their trust. Once she had successfully done that, she began to engage in phishing schemes to get more private information about them and the companies they worked for.
Armed with this information, she could more easily start to go after the company itself, using the employee or employees as the entry point. Mia Ash would then use malware to get what she wanted. The fake profile specialized in trafficking a RAT, or a Remote Access Trojan, called PupyRAT. PupyRAT was delivered to the employee via email and, when that person inside the targeted organization clicked on the link from their company email account, it would open up a document that automatically downloaded the malware onto their computer. Just like that, Mia Ash was in the company network.
Mia was eventually caught by a team dedicated to finding major cybercriminals with help from organizations that had turned down her requests to talk. ‘She’ was uncovered to be a ‘they’: Mia Ash was being operated by a cyber threat group devoted to stealing this type of information from businesses for profit.
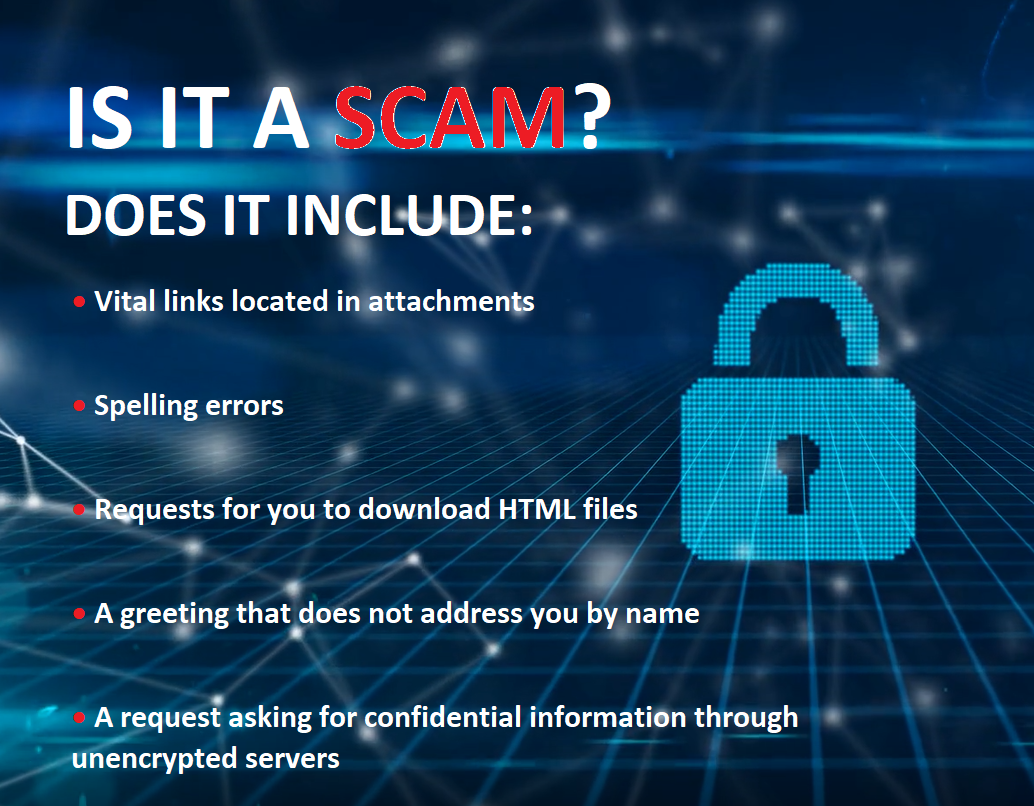
How Do I Tell It’s a Scam?
Phishing scams are all over the web! Save yourself some of the trouble of discerning which messages are real and which are fakes designed to trick you into giving up vital credentials! Beware messages from people outside of your corporate network that you weren't expecting to receive. Frequently, these unknown senders will also drop other clues that it's a scam:
Threats on Social media
Twitter has become a hotbed for spear-phishing because you do the work for the criminals; instead of having to make malware that appeals to a wide audience, they only have to get one person to fall for it. Once you’re infected, it spreads to all of your contacts and anyone else you may have interacted with online; that includes your customers, too. Tripwire reported that only 30% of spear-phishing emails are opened, so you may wonder how it becomes so prevalent. The fact is that only 30% of them need to be opened. Once it’s on someone’s computer, their account spreads it to everyone else. 66% of spear-phishing posts, even ones that are very similar to those emails that you just ignored from a stranger, get clicked on from trusted social media pages. Just because you’re smart enough to ignore traps from strangers doesn’t mean you’re prepared to be suspicious of pages that you know and trust.
Instagram experiences similar issues as Twitter. Spam and bot accounts will try to get you to follow them, likely to try and lure you into clicking on any of the virus-spreading links that they often post in their bio or as the caption underneath their pictures. Make sure you’re only following people you know and trust not to be fake accounts, and be careful of any links that take you outside of the site. These are potentially dangerous and could contain malware that you do not want spreading to your phone or computer.
LinkedIn scams take a different approach than luring you in by using a trusted user’s page. Instead, they are aimed at installing malware into your network by directing you to outside sources. Since LinkedIn is a platform that is primarily used to view others’ pages, the goal of the cybercriminals is to get you to click on a link that appears to go to someone’s page or another business’s profile, but instead redirects you to an entirely different page, where they then automatically install malware onto your computer—often, in the background without you even knowing that anything installed onto your computer at all.

Time To Take Action
Phishing scams can do more than just sabotage your accounts, they may be gateways to downloading malware that affects the entire system. Beware!
If you are concerned your place of business does not have the adequate protections in place to detect and deter cyber security threats, contact America One Technologies today and request a FREE Cyber Security assessment (a $299 value). We will let you know where your IT security infrastructure stands when it comes to information security and suggest remedies to protect you from an unexpected attack. Call America One at (781) 356-3535 or schedule a 10-minute call below to request your FREE assessment today!